If you’re like me, you’ve probably accumulated a plethora of access tokens over the past months for services like Speckle, Google Cloud, GitHub, OpenAI, and more.
Why Review and Manage Access Tokens?
While access tokens are inherently secure, it’s crucial to understand their role in safeguarding our digital environments. These tokens act as keys to our online presence and data. Just as we wouldn’t leave physical keys lying around, digital keys need careful management, too.
- Reduced Security Risks: Unused or forgotten tokens can become vulnerabilities. Malicious actors may exploit them if they somehow gain access to them. Regularly reviewing and removing old tokens can significantly lower this risk.
- Minimized Permission Footprint: Often, we grant broad permissions when creating tokens. However, following the principle of least privilege is essential. By issuing tokens only with the permissions necessary for a specific task, we reduce the potential damage in case of a token compromise.
- Better Organization and Control: Regularly auditing your tokens can help maintain an organized and manageable set of credentials. It ensures that only active and necessary tokens are circulated, making monitoring and management more straightforward.
How to Manage Your Tokens Effectively?
- Regular Audits: Set a routine, perhaps at the start of each year, to review all your access tokens. Check their purpose, usage, and whether they are still needed.
- Scope Management: When creating new tokens, critically assess the permissions you grant. Aim for the minimum level of access necessary for the task at hand.
- Secure Storage: Use reliable password managers like LastPass or 1Password. They provide secure storage and organization, with options to name and describe each token.
Where to Manage Your Speckle Tokens?
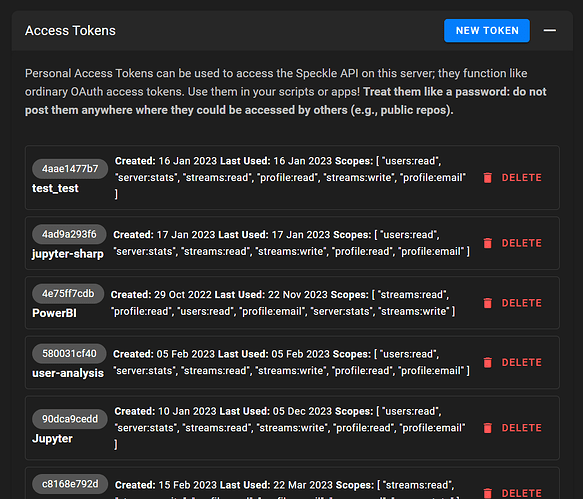
For those using Speckle, you can manage your tokens at speckle.xyz/profile for FE1 or app.speckle.systems/developer-settings for FE2.
Final Thoughts
As we enter the new year, let’s take this as an opportunity to enhance our digital security practices. A small effort in managing access tokens can go a long way in protecting our online environments. Let’s start this year with a clean, secure, organized digital slate!
and so on I’m sure I’m no longer needing that test_test token